How Unattended IoT Infrastructure Risk Is Quietly Rewriting Crime, Security, and Social Behaviour
Unattended IoT infrastructure risk is one of the least discussed and most consequential challenges facing the connected technology industry today. Over the last decade, convenience has become the dominant force shaping how we design, deploy, and operate physical infrastructure. Not comfort. Not luxury. Convenience. We optimise for fewer clicks, fewer people, fewer barriers, fewer delays. And IoT makes that optimisation possible at scale.
Cellular connectivity, remote management platforms, unattended endpoints, mobile authentication, QR codes, and cloud control have enabled an entire class of infrastructure that simply did not exist ten years ago. Parcel lockers are one of the most visible examples of this shift, but they are not unique. They are merely the most familiar.
Behind them lies a deeper pattern that affects everything from EV charging and CCTV to smart city cabinets, roadside telecoms, and remote monitoring systems. This article examines that pattern honestly: how IoT-powered convenience reshapes not only operations and cost, but crime, behaviour, and risk itself.
Convenience is not neutral
Convenience is often framed as an unqualified good. Faster. Easier. Always available.
But convenience is not neutral. It changes incentives, behaviours, and expectations. When applied at scale through IoT, it also reshapes the threat landscape. When we remove friction for legitimate users, we almost always remove friction for attackers too.
This is not a failure of IoT. It is a property of it. And understanding that distinction is essential for anyone designing, deploying, or procuring connected infrastructure.
The rise of unattended infrastructure
Before IoT, most infrastructure was attended by default. Shops had staff. Depots had gates. Cabinets were locked and physically checked. Systems failed loudly and visibly, in front of people who could respond.
IoT and cellular connectivity changed that equation. Now we routinely deploy devices with no local supervision, assets accessible around the clock, systems authenticated remotely, and infrastructure expected to operate indefinitely without human presence. The parcel locker is the clearest public example of this model — always on, always connected, always unattended, always predictable in location and behaviour — but the same pattern exists across modern IoT.
What the data tells us
Over the past two years, three trends have risen together. Individually, each looks like a story about its own sector. Together, they reveal the structural nature of unattended IoT infrastructure risk.
Parcel theft is getting worse — and more valuable
Quadient’s FOI-based Parcel Theft Report shows the estimated value of parcels stolen in the UK rising from roughly £376 million in the year to June 2024 to £666 million in the year to June 2025. That is not a gentle increase. It is a near-doubling in twelve months. The number of households affected rose 31% year-on-year to 4.83 million, and the average value per stolen parcel climbed from £102 to £138.
This is not just more theft. It is more valuable theft, affecting more people, more often.
| Metric | Year to Jun 2024 | Year to Jun 2025 | Change |
|---|---|---|---|
| Estimated value of stolen parcels | £376 million | £666 million | +77% |
| Households affected | 3.69 million | 4.83 million | +31% |
| Average value per stolen parcel | £102 | £138 | +35% |
Source: Quadient Parcel Theft Report (FOI-based estimates)
Locker infrastructure is expanding rapidly
In the same period, locker networks expanded aggressively. InPost’s UK locker footprint grew from approximately 9,200 units at the end of 2024 to over 13,700 by the end of 2025 — a 48% increase in a single year. Each locker is an efficiency win, reducing failed deliveries, cutting last-mile costs, and giving consumers flexible collection options. Each locker is also a new unattended asset, deployed into supermarket car parks, petrol forecourts, and public spaces.
| InPost UK Locker Count | End of Year | YoY Growth |
|---|---|---|
| 2023 | ~6,200 | — |
| 2024 | ~9,200 | +48% |
| 2025 | ~13,700 | +48% |
Source: InPost Group financial reporting
The growth is understandable. Doorstep theft drives demand for secure alternatives. But when the alternative is an unattended metal cabinet in an empty car park at 2am, the security calculation is not as simple as it first appears.
Digital fraud and social engineering have surged
Meanwhile, the digital side has accelerated sharply. Ofcom reported approximately 100 million suspicious messages flagged to mobile operators via the 7726 reporting service in the year to April 2025, and research showed that 50% of UK mobile users received a suspicious message between November 2024 and February 2025. Cifas data showed facility and account takeover fraud jumping hard through 2024 and remaining elevated through the first half of 2025, with telecommunications a major target sector.
This matters because parcel delivery has become one of the most effective social engineering narratives in the UK. “Missed parcel” texts, fake collection links, QR code phishing, and account takeover via email and mobile number are now routine. The parcel journey has become an identity journey, and mobile identity has become the weakest link — not because the technology is broken, but because it is now central to everything.
These three trends are not coincidental
Rising theft creates demand for lockers. Locker expansion creates new unattended targets. Digital fraud exploits the identity systems that make lockers work. Each trend feeds the others. Understanding them in isolation misses the point.
The three layers of unattended IoT infrastructure risk
A modern parcel locker is not just a metal box. It is an IoT system: cellular modem, backend platform, remote authentication, mobile or app-based identity, and centralised fleet management. This architecture enables massive convenience — no staffing, no fixed connectivity, rapid rollout, minimal operating cost. But it also creates a new crime surface across three distinct layers.
| Threat Layer | Attack Method | Example | Amplifier |
|---|---|---|---|
| Physical | Forced entry, tools, vehicle impact | Locker raids, cabinet break-ins, cable theft | Predictable locations, overnight isolation |
| Digital | Phishing, account takeover, SIM swap | Fake “missed parcel” SMS, code interception | Mobile identity as single point of failure |
| Social | Content sharing, method broadcasting | TikTok videos of exploits, Facebook group tips | Instant reach, zero-cost replication |
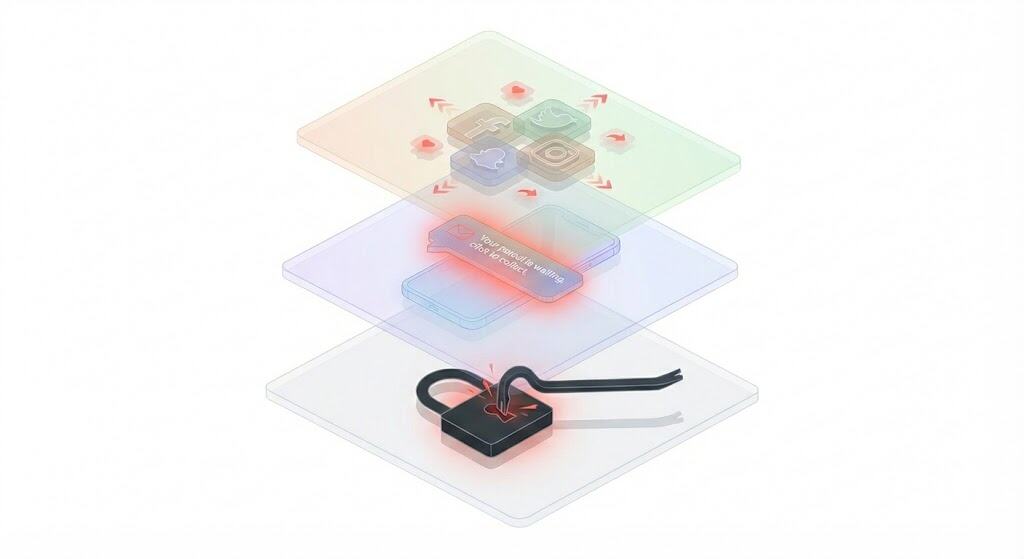
These three layers do not operate independently. They reinforce each other, and any serious assessment of unattended IoT infrastructure risk must account for all three simultaneously.
Physical crime
An unattended locker concentrates value in a predictable location, often overnight, often in low-visibility environments. The Radcliffe Lidl raid that prompted the original discussion behind this article is a textbook example: tools applied to a known target, in an empty car park, at a predictable time.
This mirrors patterns seen across IoT infrastructure — ATM vandalism, copper theft from telecoms cabinets, EV cable theft, roadside enclosure break-ins. The progression is consistent. The first incident is opportunistic. The second is deliberate. The third is systematic.
Once a location is successfully attacked, that knowledge does not stay local. It spreads.
Digital crime
Locker usage is tightly coupled to mobile identity. SMS notifications, app logins, QR codes, email confirmations — each touchpoint is an attack surface. Sophisticated attackers no longer need to defeat the locker physically. They can defeat the identity layer instead, intercepting collection codes, taking over accounts, or rerouting parcels before the legitimate recipient even knows they have arrived.
SIM swap attacks, where a criminal transfers a victim’s phone number to a new SIM card, are particularly relevant here. When your mobile number is the key to your parcel locker, your email, your banking, and your retail accounts, compromising that single factor compromises everything downstream.
Social amplification
Unlike older infrastructure, failures and exploits in locker systems are now broadcast instantly. Videos of forced lockers appear on TikTok. Posts in local Facebook groups detail which locations are vulnerable. Screenshots circulate on WhatsApp showing exactly how attacks work. Crime has always been learnable, but social media has made it learnable at scale, with near-zero effort. A successful attack in Radcliffe becomes a template for someone in Rotherham, Reading, or Rhyl within hours.
This social amplification effect is profoundly underestimated by operators and security teams accustomed to thinking about physical deterrence and digital controls. When your crime prevention strategy does not account for the fact that every weakness will be broadcast to millions of people, it is not a strategy. It is a hope.
The hidden cost of removing people
The most significant change IoT brings to infrastructure is not technological. It is the removal of human presence.
People do more than operate systems. They deter crime simply by existing. They introduce unpredictability into environments that would otherwise be entirely predictable. They notice things that sensors miss. They escalate issues early, before they become patterns.
When we remove people, detection becomes delayed, response becomes remote, and deterrence becomes theoretical. A CCTV camera that records but does not intervene is not a deterrent. A sign warning of prosecution is not a deterrent. An insurance policy is not a deterrent. These are after-the-fact mechanisms — useful for recovery, useless for prevention.
Convenience replaces friction. Security requires friction. That tension is fundamental to every IoT deployment, and pretending it does not exist is how systems fail.
Risk does not disappear. It relocates.
One of the most important insights for anyone assessing unattended IoT infrastructure risk is this: IoT rarely removes risk. It moves it.
| Risk moves from… | …to |
|---|---|
| Staffing costs | Insurance claims |
| Guarded locations | Distributed unattended assets |
| Visible failure | Silent compromise |
| Physical theft | Identity abuse |
| Operator’s balance sheet | Customer’s loss |
Parcel lockers did not eliminate parcel theft. They shifted where and how it happens. Just as CCTV did not eliminate vandalism, and EV charging did not eliminate cable theft. The pattern repeats across every category of unattended connected infrastructure.
The insurance moral hazard
There is a sharper point here that the industry is reluctant to confront. When operators treat insurance as their primary security strategy, they create a moral hazard. If every theft is covered by a claim, the financial incentive to prevent theft weakens. The operator’s cost-benefit analysis quietly concludes that paying premiums is cheaper than paying for physical hardening, better placement, monitored CCTV, or tamper detection.
This calculation is rational in the short term. It is corrosive in the long term. Insurance does not reduce crime. It funds tolerance of crime. And that tolerance eventually erodes public trust, increases premiums industry-wide, and externalises the real cost onto customers, police forces, and communities.
Why scale changes everything
At small scale, the issues described here feel manageable. One locker attacked. One cabinet damaged. One charger vandalised. Annoying, but containable.
At scale, they become systemic. And IoT excels at scale. A single design weakness — a lock mechanism that yields to a specific tool, an authentication flow vulnerable to interception, a placement pattern that creates predictable blind spots — multiplied across thousands of identical deployments, becomes an industry-wide problem overnight.
This is why “rare incidents” suddenly appear everywhere. They were never rare. They were waiting for scale to reveal them. The efficiency that makes IoT economically viable — standardised hardware, identical configurations, templated deployments — is the same efficiency that makes it structurally vulnerable.
Convenience as a social contract
There is a social dimension here that is rarely discussed in technical or industry contexts.
Convenience changes expectations. Access should be instant. Systems should be available around the clock. Friction feels unfair, even punitive. Once people are conditioned to frictionless experiences, any reintroduction of friction — delays, restrictions, human checks, limited access windows — feels like regression. Like something has been taken away.
This creates a ratchet effect. It becomes harder to roll back risky designs, even when the data clearly says we should, because the user expectation has already been set. A locker operator who restricts overnight access to reduce theft will lose customers to a competitor who does not. An EV network that adds physical barriers to prevent cable theft will be criticised for making charging less convenient.
The result is an industry that consistently underprices security because the market punishes friction more visibly than it punishes risk.
Who should be in the room when convenience is designed
This is where the IoT industry has a structural blind spot, and it matters more than any single technical fix.
Most unattended IoT products — lockers, chargers, monitoring systems, smart cabinets — are designed by teams that are good at what they do: industrial design, embedded engineering, cloud platform development, cellular connectivity. They build a product, add a SIM, connect it to a backend, and deploy it at scale. The engineering works. The connectivity works. The platform works.
What does not work is the assumption that engineering and connectivity are sufficient.
The product gets designed. The security gets assumed. The deployment environment gets underestimated. The crime surface gets discovered after launch, not before it.
This happens because the people who understand the operational reality — the threat landscape, the physical environment, the way criminal behaviour adapts, the fragility of mobile identity, the limitations of remote monitoring — are rarely in the room when the product is conceived.
The disciplines that should be involved but usually are not
Physical security and crime prevention specialists. Not cybersecurity consultants. People who understand how physical assets are attacked in public environments — the tools, the timing, the reconnaissance patterns. Designing Out Crime Officers (DOCOs), loss prevention specialists, and people with practical experience of infrastructure vandalism and theft. They know that a locker in a lit, staffed forecourt and a locker in an unmonitored car park are not the same product, even if the hardware is identical.
Telecommunications and connectivity architects. Not just the team that provisions the SIM card. People who understand cellular network resilience, signal environments, failover behaviour, and the security implications of relying on mobile identity for authentication. The connectivity layer is not a commodity add-on. It is the nervous system of the entire deployment, and its design has direct implications for tamper detection, alert escalation, and identity verification.
Experienced IoT deployment consultants. People who have seen what actually happens when connected infrastructure meets the real world. Not in a lab, not in a pilot, but across hundreds of sites over years. They know which cabinet gets flooded, which pole gets hit, which car park gets targeted, and which firmware update bricks a fleet. This is not theoretical knowledge. It is operational scar tissue, and it is irreplaceable.
Insurance and liability specialists. Not to write the policy after launch, but to model the risk before design is finalised. If the insurance assessment says “this deployment profile will generate X claims per thousand units per year,” that information should shape the product, not just the premium.
Site hosts and local stakeholders. The supermarket security manager. The council highways team. The facilities contractor. These are the people who understand the environment where the product will actually live, and they almost never see the product until it arrives on a flatbed truck.
Why this matters
The pattern across the industry is consistent. A product team builds something that works technically, a sales team sells it at scale, and an operations team discovers the real-world problems twelve months later. By then, thousands of units are deployed, the design is locked, and the cost of remediation is orders of magnitude higher than the cost of getting it right in the first place.
The companies that will lead the next generation of unattended IoT infrastructure are not the ones with the best cloud platform or the cheapest hardware. They are the ones that understand the deployment environment as deeply as they understand the technology, because they put the right people in the room at the start.
Building a locker and adding a SIM card does not make you an IoT infrastructure company. Understanding what happens to that locker at 2am in a dark car park, and designing for it — that does.
What this means for anyone procuring or specifying IoT infrastructure
The dynamics described in this article are not theoretical. They affect procurement decisions, site planning, vendor evaluation, and total cost of ownership calculations today.
If you are specifying or buying unattended connected infrastructure — whether that is parcel lockers, EV chargers, CCTV systems, telecoms cabinets, or environmental monitoring equipment — the following questions should be part of your evaluation.
| Evaluation Area | Key Question | What to look for |
|---|---|---|
| Physical resilience | What happens when this is attacked, not if? | Tested forced-entry resistance, not just IP/IK ratings |
| Detection and response | Does it detect tampering in real time? | Contracted response SLAs, not assumed escalation |
| Placement and environment | Is the location attended or isolated at night? | Genuine CCTV coverage, lighting, proximity to staff |
| Identity and authentication | What if a mobile number or email is compromised? | Fallback auth methods, not single-factor dependency |
| Insurance vs. deterrence | Is insurance replacing prevention? | Design investment in hardening, not just premium budgets |
| Scale vulnerability | Does one exploit work across the entire fleet? | Variation in security, not uniform vulnerability |
These are not comfortable questions. But they are significantly cheaper to ask before deployment than after the first systematic attack.
Designing honest convenience
The solution to the problems described here is not less IoT. It is not a retreat from cellular connectivity or unattended infrastructure. These technologies deliver genuine value, and the demand for convenience is real and legitimate.
The solution is honest design. That means acknowledging trade-offs upfront rather than discovering them through loss.
It means accepting that security is not a feature you add after deployment. It is a cost structure you either pay upfront — in design, materials, placement, monitoring, and response capability — or pay repeatedly afterwards in theft, damage, fraud, customer loss, and trust erosion.
It means recognising that “rare incidents” at small scale become systemic failures at large scale, and designing for the scale you intend to reach, not the scale you are at today.
It means understanding that removing people from infrastructure removes more than labour cost. It removes deterrence, context, unpredictability, and the ability to intervene before a pattern becomes entrenched.
And it means being willing to introduce small amounts of deliberate friction — slightly less convenient access, slightly more robust authentication, slightly more considered placement — when the evidence shows that frictionless design creates disproportionate risk.
Lessons for the wider IoT industry
Parcel lockers are not the outlier in this story. They are the warning sign.
The same dynamics — physical vulnerability, identity exploitation, social amplification, insurance dependency, scale fragility — apply to every category of unattended connected infrastructure. EV charging networks. Smart city sensor deployments. Remote CCTV cabinets. Solar and battery monitoring systems. Telecoms roadside equipment. Temporary construction IoT. Agricultural monitoring.
Any system that is unattended, predictable, connected, and scaled rapidly will eventually face the same questions. The only variable is timing.
The most mature IoT deployments are not the most frictionless ones. They are the ones that understand exactly what convenience costs, and decide deliberately whether it is worth paying.
Frequently asked questions
What is unattended IoT infrastructure?
Unattended IoT infrastructure refers to any connected system designed to operate without on-site human supervision. This includes parcel lockers, EV chargers, smart city sensor platforms, remote CCTV cabinets, telecoms enclosures, solar monitoring systems, and environmental sensors. These systems typically use cellular connectivity for remote management and are expected to function continuously without regular physical visits.
Why does convenience create security risk in IoT deployments?
When IoT systems are designed to maximise convenience, they remove friction — human presence, physical barriers, access restrictions, manual checks. These same friction points are what traditionally deterred crime and enabled rapid response to incidents. Removing them for legitimate users simultaneously removes them for attackers. The system becomes predictable, accessible, and unmonitored — conditions that criminal activity thrives on.
Is parcel locker theft increasing in the UK?
Yes. Quadient’s FOI-based research shows the estimated value of stolen parcels in the UK rose from £376 million in the year to June 2024 to £666 million in the year to June 2025, with 4.83 million households affected. Meanwhile, physical attacks on locker infrastructure — including forced entry raids on units in supermarket car parks — have been reported in multiple UK locations.
How does mobile identity relate to parcel locker security?
Modern parcel lockers rely on mobile identity for authentication — SMS notifications, app-based logins, QR codes, and email confirmations. This creates a digital attack surface alongside the physical one. Phishing messages disguised as delivery notifications, account takeover, and SIM swap attacks all exploit this dependency. Attackers can intercept collection codes or reroute parcels without ever touching the physical locker.
What is the insurance moral hazard in IoT deployments?
When operators rely on insurance as their primary security strategy rather than investing in prevention, they create a situation where the financial incentive to reduce crime weakens. Insurance covers losses after the fact but does nothing to deter attacks. Over time, this approach increases premiums industry-wide, erodes public trust, and externalises the real cost of inadequate security onto customers, police forces, and communities.
Does unattended IoT infrastructure risk only apply to parcel lockers?
No. The same risk dynamics apply to any unattended, connected, predictable, rapidly scaled infrastructure. EV charging networks, smart city deployments, remote CCTV cabinets, roadside telecoms equipment, solar and battery monitoring, temporary construction IoT, and agricultural monitoring all face the same fundamental trade-offs between convenience and security.
How can unattended IoT infrastructure risk be reduced?
Effective risk reduction requires honest design — acknowledging trade-offs upfront rather than discovering them through loss. This includes investing in physical hardening, real-time tamper detection, considered site placement, multi-factor authentication, contracted response SLAs, and involving physical security specialists, experienced deployment consultants, and telecommunications architects in the design process from the beginning. Small amounts of deliberate friction, such as restricted overnight access or stronger authentication, can dramatically reduce risk without eliminating the convenience that makes IoT deployments valuable.
Who should be involved in designing unattended IoT products?
Beyond the core engineering team, the design process should involve physical security and crime prevention specialists, telecommunications and connectivity architects, experienced IoT deployment consultants with real-world operational knowledge, insurance and liability modellers, and site hosts or local stakeholders who understand the deployment environment. Most unattended IoT infrastructure failures stem not from technology problems but from the absence of these perspectives during design.
Published on IoT Portal. This article is part of our Insight series examining the real-world implications of connected infrastructure deployment in the UK.
About The Author
Nick Appleby brings over 25 years of hands-on experience in telecommunications, cellular connectivity, and IoT infrastructure. He has founded and led successful businesses in the sector, and created industry-leading connectivity products that remain widely deployed across the UK today. He now writes independently through IoT Portal, drawing on real-world operational knowledge to examine how connected infrastructure actually performs once it leaves the lab.
